博客
主页 » 博客
Understanding the Difference Between a KVM Switch and Serial Console
Posted on June 1, 2017 by Gento

At first glance, KVM switches and serial consoles can seem quite similar. Both are tools for managing your IT infrastructure. However, the difference between them comes down to what types of equipment each tool can manage. When you understand the capabilities of each, you get a better idea of which is the right tool for the job.
iX7 Advance Controller: What You Need to Know About “Dual Networking”
Posted on May 30, 2017 by Gento

The fact of the matter is that there is no "one size fits all" solution to data center management. Very often important decisions are made based on the needs of the end users, the long-term objectives of the facility and more. Previous generation hardware, however, did little to support these needs - often forcing data center managers to adapt to the way their technology had to work instead of the other way around.
How Raritan’s KVM-Over-IP Switch Is Being Used in Astrophysical Observatory
Posted on May 25, 2017 by Gento
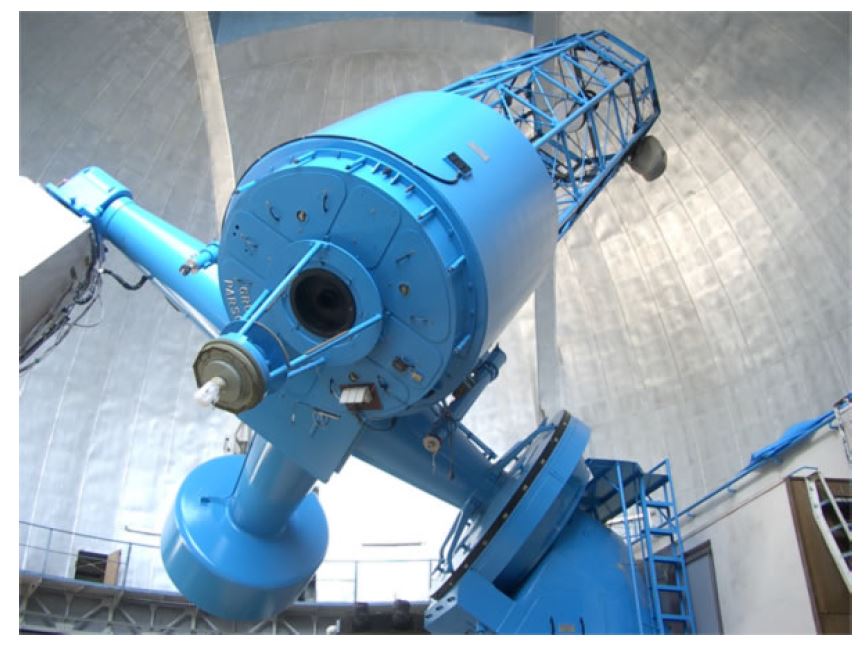
Up until recently, the Okayama Astrophysical Observatory in Japan had been operating in what they call a "classical mode." A principal investigator and/or team members would come to the observatory operate the telescope and instruments collecting all relevant data of interest and go on their way. The observing console consisted of three PCs, keyboards, mouse, speakers, six Full-HD monitors and some other related equipment.
ASHRAE’s New Energy Standard for Data Centers
Posted on May 23, 2017 by Gento

As we become more firmly entrenched in the digital revolution with each passing day, energy efficiency and general energy standards in mission-critical facilities like data centers are becoming more important all the time. Not only do factors like proper thermal design and installation practices prevent the possibility of issues like overheating or a loss of functionality, but they also allow for the facilities themselves to operate in a much more reliable and cost-effective way.
Dominion KX III KVM-over-IP Switch: Who Wants Java-Free?
Posted on May 18, 2017 by Gento

If you had to make a list of all customer complaints related to KVM and KVM-over-IP switches over the last few years, Java would undoubtedly be right at the top. There was a time where Java was a workhorse for software developers. It's safe to say that those days are now long gone. Java is one of the leading contributors to situations where KVM sessions may load incorrectly (or not at all). Java has security issues with today’s browsers, seemingly unending number of annoying pop-ups and has become infamous over the years for the types of random, forced updates that can stifle productivity in an instant.
力登官方微信公众号
力登官方微信公众号

近期活动
- New Zealand Cloud & Datacenter Convention 2022
- 3 November 2022, 9am – 4pm • Grand Millennium Hotel, Auckland, New Zealand
- Data Centre World Singapore
- 12th – 13th Oct 2022
- Korea Cloud & Datacenter Convention 2022
- 6th Oct 2022
- Philippines Cloud & Datacenter Convention 2022
- 4th Aug 2022
- JANOG50 Meeting Hokkaido
- 3th – 15th July 2022
力登最新新闻
- 重振数据中心行业—罗格朗重磅推出两款革命性的智能机架式PDU!
- Posted on May 1, 2023
- 独家专访丨惠州如何升级制造业?法资企业CEO提了个建议
- Posted on December 2, 2021
- 力登公司推出MasterConsole®数字双显示器KVM切换器
- Posted on February 18, 2021
- Legrand Data, Power and Control Division Announced as Finalist in Six Categories at DCS Awards 2020
- Posted on November 9, 2020
- 力登公司(Raritan)推出新型智慧型机架控制器(SRC),用于智能地管理数据中心和关键基础设施中的环境和安全信息
- Posted on November 9, 2020